This PowerShell script is one of the most comprehensive you will find that provides a thorough overview and full report of all group objects in a domain. It is the culmination of many Active Directory audit and reviews and therefore contains valuable input from many customers.
A lot of thought has been put into the logic within this script to help an organisation understand:
- A breakdown of each group type (category and scope) that have been created
- Groups with no members
- Groups that are flagged as critical system objects
- Groups that are protected objects (AdminSDHolder) where their adminCount attribute is set to 1
- Groups that are conflicting/duplicate objects (name contains CNF: and/or sAMAccountName contains $Duplicate)
- Groups that are mail-enabled
- Distribution groups that are mail-disabled
- Groups that are Unix-enabled
- Groups that have expired
- Groups with SID history
- Groups with no Manager (managedBy)
- The non-“Microsoft” default groups that have been left in the default Users container
FYI:
- Mail-enabled groups are derived from the proxyAddresses, legacyExchangeDN, mailNickName, and reportToOriginator attributes, where reportToOriginator must be set to TRUE. This is not well documented.
- Unix-enabled groups are derived from the gidNumber, msSFU30Name, and msSFU30NisDomain attributes.
Open the full CSV report in Excel and add a column filter and freeze the top row. This will help you to filter the data and move through the spreadsheet with ease.
Review the value of groups that contain no members, are not critical system objects, protected objects (AdminSDHolder), and not excluded objects. Delete them if they are no longer serving their purpose. Alternatively, move them into an OU and add the OU to the $ExclusionOUs array in the script to ensure they are correctly flagged in the next run.
Disabling groups:
- Security groups can be disabled by converting them to a distribution group.
- Distribution groups can be disabled by mail-disabling them.
You should always clearly document situations where groups have been disabled. i.e. Are they being kept for a reason, or should they be deleted. Delete them if they no longer serve a purpose.
Review the groups that have been marked as protected objects (AdminSDHolder) that may now fall out of scope. If these groups are not going to be deleted, they should be restored to their original state by reactivating the inheritance rights on the object itself and clearing the adminCount attribute. I recommend using a script written by Tony Murray to clean up the AdminSDHolder: Cleaning up AdminSDHolder orphans
Further information about the AdminSDHolder can be found here:
- AdminSDHolder, Protected Groups and Security Descriptor Propagator
- AdminSDHolder, Protected Groups and SDPROP
- AD Permissions : The AdminSDHolder Mechanism
- Five common questions about AdminSdHolder and SDProp
Groups whose name contains CNF: and/or sAMAccountName contains $Duplicate means that it’s a duplicate account caused by conflicting/duplicate objects. This typically occurs when objects are created on different Read Write Domain Controllers at nearly the same time. After replication kicks in and those conflicting/duplicate objects replicate to other Read Write Domain Controllers, Active Directory replication applies a conflict resolution mechanism to ensure every object is and remains unique. You can’t just delete the conflicting/duplicate objects, as these may often be in use. You need to merge the group membership and ensure the valid group is correctly applied to the resource. Then you can confidently delete the conflicting/duplicate group.
You should never delete groups marked as Critical System Objects.
There should be no groups with an unrecognised group type. But if there are any, they must be investigated and remediated immediately as they could be the result of more serious issues.
Some groups may simply be placeholders for certain tasks, scripts and policies, and therefore may purposely not contain any members. Simply move these groups into an OU and add the OU to the $ExclusionOUs array to flag and exclude them from the final no members count.
In general add groups and OUs to the ‘Exclusion’ arrays to flag and exclude groups with no members from the final no members count.
From here you can start to implement some good policies and processes around the usage and management of the groups.
At the end of the day a nice way to manage groups is to set their expirationTime attribute. This will give us the ability to implement a nice life cycle management process. You can go one step further and add a user or mail-enabled security group to the managedBy attribute. This will give us the ability to implement some workflow when the group is x days before expiring.
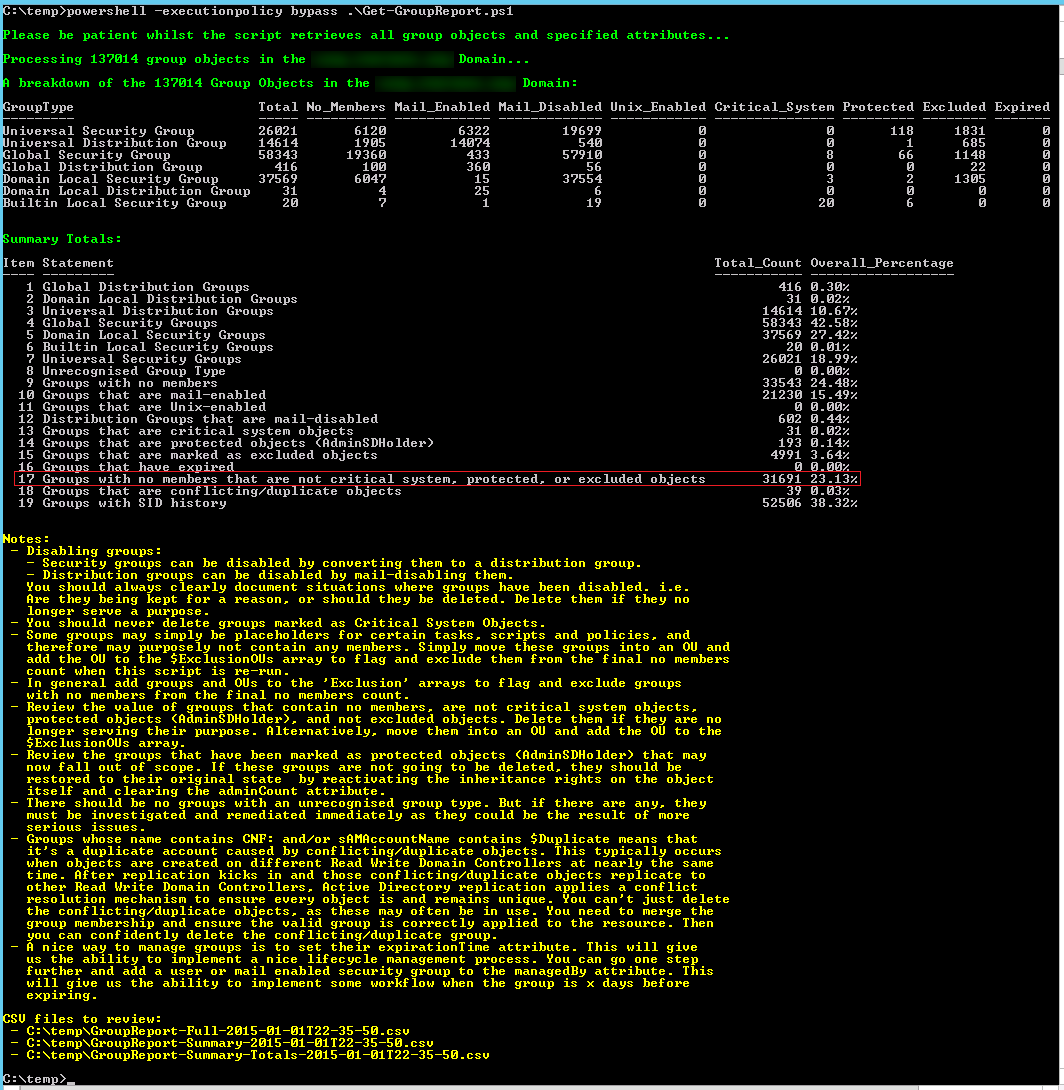
The following screen shot is from a recent health check and audit I completed. This customer has about 137,000 group objects in their domain. The script took about 2 and a half hours to complete. PowerShell consumed almost 8 GB of RAM. The full CSV report was about 55.5 MB.
What sticks out here like a sore thumb is the fact that over 23% of the groups have no members!
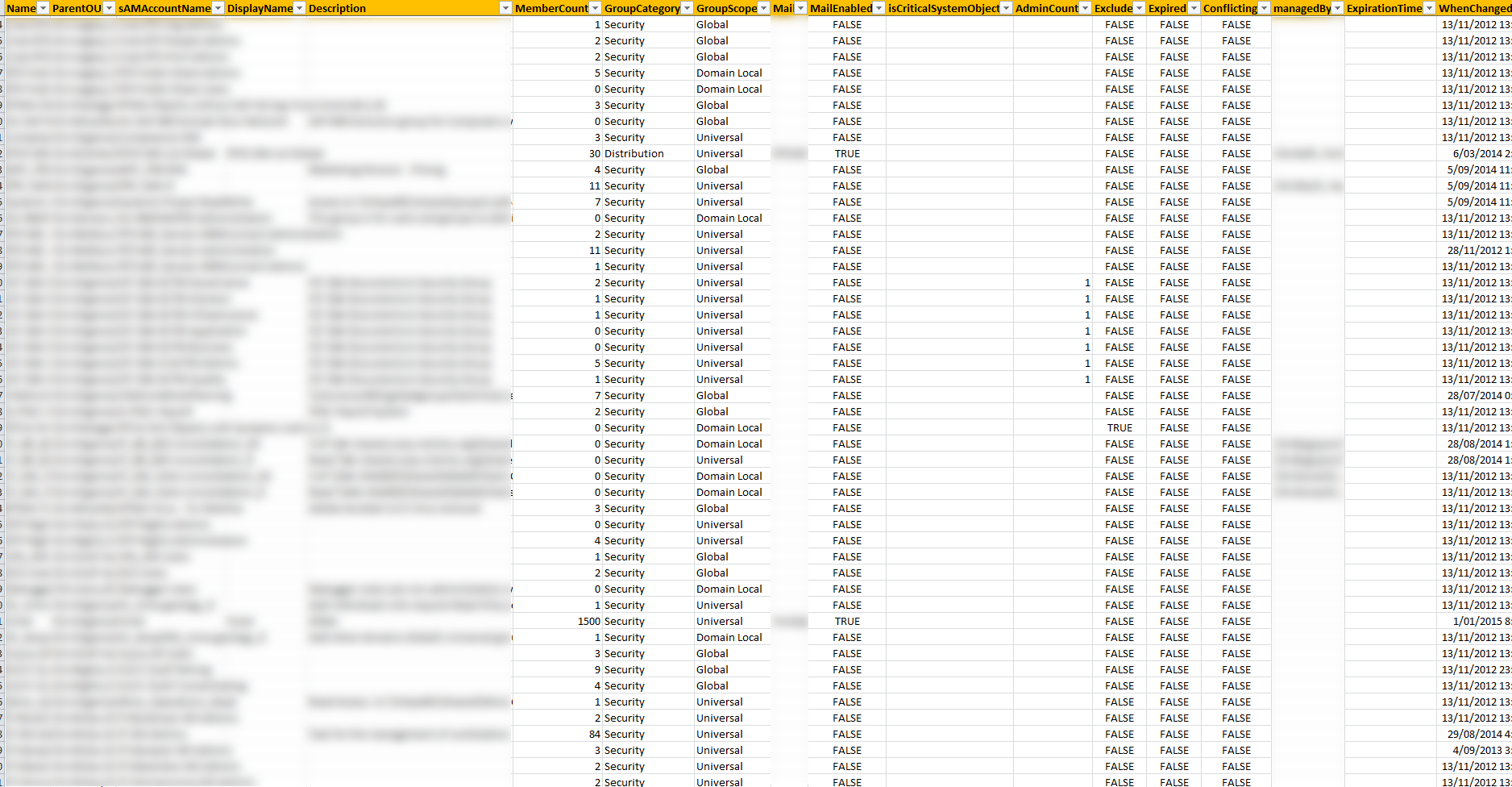
The following screen shot is the full report from the same health check. Whilst I’ve had to blur our some of the data you can get an idea from the column headings that it’s fairly extensive. There are a further 6 columns that I was unable to capture in the screen shot due to screen resolution.
IMPORTANT: As of version 1.8 this script now works in non Microsoft Exchange environments.
Here is the Get-GroupReport.ps1 (2763 downloads) script:
001 002 003 004 005 006 007 008 009 010 011 012 013 014 015 016 017 018 019 020 021 022 023 024 025 026 027 028 029 030 031 032 033 034 035 036 037 038 039 040 041 042 043 044 045 046 047 048 049 050 051 052 053 054 055 056 057 058 059 060 061 062 063 064 065 066 067 068 069 070 071 072 073 074 075 076 077 078 079 080 081 082 083 084 085 086 087 088 089 090 091 092 093 094 095 096 097 098 099 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 332 333 334 335 336 337 338 339 340 341 342 343 344 345 346 347 348 349 350 351 352 353 354 355 356 357 358 359 360 361 362 363 364 365 366 367 368 369 370 371 372 373 374 375 376 377 378 379 380 381 382 383 384 385 386 387 388 389 390 391 392 393 394 395 396 397 398 399 400 401 402 403 404 405 406 407 408 409 410 411 412 413 414 415 416 417 418 419 420 421 422 423 424 425 426 427 428 429 430 431 432 433 434 435 436 437 438 439 440 441 442 443 444 445 446 447 448 449 450 451 452 453 454 455 456 457 458 459 460 461 462 463 464 465 466 467 468 469 470 471 472 473 474 475 476 477 478 479 480 481 482 483 484 485 486 487 488 489 490 491 492 493 494 495 496 497 498 499 500 501 502 503 504 505 506 507 508 509 510 511 512 513 514 515 516 517 518 519 520 521 522 523 524 525 526 527 528 529 530 531 532 533 534 535 536 537 538 539 540 541 542 543 544 545 546 547 548 549 550 551 552 553 554 555 556 557 558 559 560 561 562 563 564 565 566 567 568 569 570 571 572 573 574 575 576 577 578 579 580 581 582 583 584 585 586 587 588 589 590 591 592 593 594 595 596 597 598 599 600 601 602 603 604 605 606 607 608 609 610 611 612 613 614 615 616 617 618 619 620 621 622 623 624 625 626 627 628 629 630 631 632 633 634 635 636 637 638 639 640 641 642 643 644 645 646 647 648 649 650 651 652 653 654 655 656 657 658 659 660 661 662 663 664 665 666 667 668 669 670 671 672 673 674 675 676 677 678 679 680 681 682 683 684 685 686 687 688 689 690 691 692 693 694 695 696 697 698 699 700 701 702 703 704 705 706 707 708 709 710 711 712 713 714 715 716 717 718 719 720 721 722 723 724 725 726 727 728 729 730 731 732 733 734 735 736 737 738 739 740 741 742 743 744 745 746 747 748 749 750 751 752 753 754 755 756 757 758 759 760 761 762 763 764 765 766 767 768 769 770 771 772 773 774 775 776 777 778 779 780 781 782 783 784 785 786 787 788 789 790 791 792 793 794 795 796 797 798 799 800 801 802 803 804 805 806 807 808 809 810 811 812 813 814 815 816 817 818 819 820 821 822 823 824 825 826 827 828 829 830 831 832 833 834 835 836 837 838 839 840 841 842 843 844 845 846 847 848 849 850 851 852 853 854 | <# This script will enumerate all group objects in a Domain, providing both a high level overview and a full report based on the values of the following attributes: - name - distinguishedname - samaccountname - mail - grouptype - displayname - description - member - memberof - info - isCriticalSystemObject - admincount - managedBy - expirationtime (requires Exchange Schema Extensions) - whencreated - whenchanged - sidhistory - objectsid - proxyAddresses (requires Exchange Schema Extensions) - legacyExchangeDN (requires Exchange Schema Extensions) - mailNickName (requires Exchange Schema Extensions) - reportToOriginator (requires Exchange Schema Extensions) - gidNumber - msSFU30Name - msSFU30NisDomain We further derive: - The Parent OU from the distinguishedname attribute. - The GroupCategory and GroupScope from the grouptype attribute. - The MemberCount from the member attribute. - MailEnabled from proxyAddresses, legacyExchangeDN, mailNickName, and reportToOriginator. reportToOriginator must be set to TRUE. This is not well documented. - Expired from the expirationtime attribute. - Conflict from the name and samaccountname attributes. - UnixEnabled from gidnumber, mssfu30name, mssfu30nisdomain. - Exclude: When reviewing groups it's important to flag the ones that are marked as Critical System Objects where their isCriticalSystemObject attribute is set to True, Protected Objects (AdminSDHolder) where their adminCount attribute is set to 1, and various other important groups that should not be removed. To be able to capture the "other" groups we place them into the $ExclusionGroups and $ExclusionOUs arrays. Now, you may have groups marked by the AdminSDHolder that no longer require protection. It happens due to group nesting, and is not something that's automatically removed when the group falls out of scope. Therefore it's still marked as protected. This is often unintentional and typically misunderstood. You'll need to review each one to unblock inheritance and clear the adminCount attribute where they fall out of scope. However, I recommend using a script written by Tony Murray to clean up the AdminSDHolder: http://www.open-a-socket.com/index.php/2013/09/11/cleaning-up-adminsdholder-orphans/ Further information about the AdminSDHolder can be found here: - http://social.technet.microsoft.com/wiki/contents/articles/22331.adminsdholder-protected-groups-and-security-descriptor-propagator.aspx - http://technet.microsoft.com/en-us/magazine/2009.09.sdadminholder.aspx - http://www.selfadsi.org/extended-ad/ad-permissions-adminsdholder.htm - http://blogs.technet.com/b/askds/archive/2009/05/07/five-common-questions-about-adminsdholder-and-sdprop.aspx I have seen situations where the adminCount attribute is set to 5. Whilst this is an invalid and undocumented value the adminCount attribute is 4 bytes (32 bits) in size. Valid values are 0 (disabled), 1 (enabled), or not set (disabled - default). So it's simply enabled or disabled based on the least significant bit. Converting 5 into binary, it's least significant bit is 1. Therefore, we take a setting of 5 to mean that it's enabled. We group together the following 4 attributes to determine if a group is mail-enabled: proxyAddresses, legacyExchangeDN, mailNickName, and reportToOriginator: - http://pmoreland.blogspot.com.au/2013/03/creating-mail-contacts-and-distribution.html Groups whose name contains CNF: and/or sAMAccountName contains $Duplicate means that it's a duplicate account caused by conflicting/duplicate objects. This typically occurs when objects are created on different Read Write Domain Controllers at nearly the same time. After replication kicks in and those conflicting/duplicate objects replicate to other Read Write Domain Controllers, Active Directory replication applies a conflict resolution mechanism to ensure every object is and remains unique. You can't just delete the conflicting/ duplicate objects, as these may often be in use. You need to merge the group membership and ensure the valid group is correctly applied to the resource. Then you can confidently delete the conflicting/duplicate group. In environments where the Exchange Schema has been deployed a nice way to manage groups it to set their expirationTime attribute. This will give us the ability to implement a nice lifecycle management process. You can go one step further and add a user or mail enabled security group to the managedBy attribute. This will give us the ability to implement some workflow when the group is x days before expiring. Syntax examples: - To execute the script in the current Domain: Get-GroupReport.ps1 - To execute the script against a trusted Domain: Get-GroupReport.ps1 -TrustedDomain mydemosthatrock.com Script Name: Get-GroupReport.ps1 Release 1.9 Written by Jeremy@jhouseconsulting.com 16/12/2014 Modified by Jeremy@jhouseconsulting.com 06/05/2015 #>#-------------------------------------------------------------param([String]$TrustedDomain,[switch]$verbose)Set-StrictMode -Version 2.0if ($verbose.IsPresent) { $VerbosePreference = 'Continue' Write-Verbose "Verbose Mode Enabled" } Else { $VerbosePreference = 'SilentlyContinue' }#-------------------------------------------------------------# Set this to the OU structure where the you want to search to# start from. Do not add the Domain DN. If you leave it blank,# the script will start from the root of the domain.$OUStructureToProcess = ""# Set the name of the attribute you want to populate for objects# to be evaluated as a stale or non-stale object.$ExcludeAttribute = "comment"# Set the text within the $ExcludeAttribute that you want to use# to evaluate if the object should be excluded from the stale# object collection.$ExcludeText = "Decommission=False"# Set this to the delimiter for the CSV output$Delimiter = ","# Set this to remove the double quotes from each value within the# CSV.$RemoveQuotesFromCSV = $False# Set this value to true if you want to see the progress bar.$ProgressBar = $True# Although some of the default groups are not marked as a Critical# System Objects or Protected Objects (AdminSDHolder) they must# still be excluded from deletion as a good practice.# http://technet.microsoft.com/en-us/library/dn579255.aspx# On top of this we exclude the RTC groups as part of OCS/Lync and# also the "Microsoft Exchange" OUs.$ExclusionGroups = @("DnsAdmins",`"DnsUpdateProxy",`"DHCP Users",`"DHCP Administrators",`"Offer Remote Assistance Helpers",`"TelnetClients",`"IIS_WPG",`"Access Control Assistance Operators",`"Cloneable Domain Controllers",`"Hyper-V Administrators",`"Protected Users",`"RDS Endpoint Servers",`"RDS Management Servers",`"RDS Remote Access Servers",`"Remote Management Users",`"WinRMRemoteWMIUsers_",`"RTC*")$ExclusionOUs = @("*Microsoft Exchange System Objects*""*Microsoft Exchange Security Groups*")#-------------------------------------------------------------$invalidChars = [io.path]::GetInvalidFileNamechars() $datestampforfilename = ((Get-Date -format s).ToString() -replace "[$invalidChars]","-")# Get the script path$ScriptPath = {Split-Path $MyInvocation.ScriptName}$ReferenceFileFull = $(&$ScriptPath) + "\GroupReport-Full-$($datestampforfilename).csv"$ReferenceFileSummary = $(&$ScriptPath) + "\GroupReport-Summary-$($datestampforfilename).csv"$ReferenceFileSummaryTotals = $(&$ScriptPath) + "\GroupReport-Summary-Totals-$($datestampforfilename).csv"if (Test-Path -path $ReferenceFileFull) { remove-item $ReferenceFileFull -force -confirm:$false}if (Test-Path -path $ReferenceFileSummary) { remove-item $ReferenceFileSummary -force -confirm:$false}if (Test-Path -path $ReferenceFileSummaryTotals) { remove-item $ReferenceFileSummaryTotals -force -confirm:$false}Function CheckIfExchangeSchemaIsPresent { Param($root) # This function check to see if the ms-Exch-Schema-Verison-PT attribute is present. This # test is used to determine if the Exchange Schema is present. If ($root -eq "CurrentForest" -OR $root -eq "" -OR $root -eq $NULL) { $RootDSE = [ADSI]"LDAP://RootDSE" } Else { $RootDSE = [ADSI]"LDAP://$Root/RootDSE" } $version = "CN=ms-Exch-Schema-Version-Pt,$($RootDSE.schemaNamingContext)" $value = [ADSI]::Exists( "LDAP://$version" ) return $value}if ([String]::IsNullOrEmpty($TrustedDomain)) { # Get the Current Domain Information $domain = [System.DirectoryServices.ActiveDirectory.Domain]::GetCurrentDomain()} else { $context = new-object System.DirectoryServices.ActiveDirectory.DirectoryContext("domain",$TrustedDomain) Try { $domain = [System.DirectoryServices.ActiveDirectory.Domain]::GetDomain($context) } Catch [exception] { write-host -ForegroundColor red $_.Exception.Message Exit }}# Get AD Distinguished Name$DomainDistinguishedName = $Domain.GetDirectoryEntry() | select -ExpandProperty DistinguishedName If ($OUStructureToProcess -eq "") { $ADSearchBase = $DomainDistinguishedName} else { $ADSearchBase = $OUStructureToProcess + "," + $DomainDistinguishedName}# Check if the Exchange Schema is present by calling the CheckIfExchangeSchemaIsPresent functionif ([String]::IsNullOrEmpty($TrustedDomain)) { $IsExchangePresent = CheckIfExchangeSchemaIsPresent "CurrentForest"} else { $IsExchangePresent = CheckIfExchangeSchemaIsPresent $TrustedDomain}$TotalGroupsProcessed = 0$GroupCount = 0$GlobalDistributionGroups = 0$DomainLocalDistributionGroups = 0$UniversalDistributionGroups = 0$GlobalSecurityGroups = 0$DomainLocalSecurityGroups = 0$BuiltinLocalSecurityGroups = 0$UniversalSecurityGroups = 0$UnrecognisedGroupTypes = 0$GroupsHashTable = @{}$TotalNoMembers = 0$TotalMailEnabledObjects = 0$TotalMailEnabledDistributionGroups = 0$TotalCriticalSystemObjects = 0$TotalProtectedObjects = 0$TotalExcludedObjects = 0$TotalToSubtract = 0$TotalExpiredObjects = 0$TotalConflictingObjects = 0$TotalWithSIDHistory = 0$TotalUnixEnabledObjects = 0$TotalNoManagedBy = 0# Create an LDAP search for all groups$ADFilter = "(objectClass=group)"# There is a known bug in PowerShell requiring the DirectorySearcher# properties to be in lower case for reliability.$ADPropertyList = @("name","distinguishedname","samaccountname","mail","grouptype", ` "displayname","description","member","memberof","info", ` "isCriticalSystemObject","admincount","managedBy","objectsid", ` "expirationtime","whencreated","whenchanged","sidhistory", ` "proxyaddresses","legacyexchangedn","mailnickname", ` "reporttooriginator","gidnumber","mssfu30name","mssfu30nisdomain")$ADScope = "SUBTREE"$ADPageSize = 1000$ADSearchRoot = New-Object System.DirectoryServices.DirectoryEntry("LDAP://$($ADSearchBase)") $ADSearcher = New-Object System.DirectoryServices.DirectorySearcher$ADSearcher.SearchRoot = $ADSearchRoot$ADSearcher.PageSize = $ADPageSize $ADSearcher.Filter = $ADFilter $ADSearcher.SearchScope = $ADScopeif ($ADPropertyList) { foreach ($ADProperty in $ADPropertyList) { [Void]$ADSearcher.PropertiesToLoad.Add($ADProperty) }}Try { write-host -ForegroundColor Green "`nPlease be patient whilst the script retrieves all group objects and specified attributes..." $colResults = $ADSearcher.Findall() # Dispose of the search and results properly to avoid a memory leak $ADSearcher.Dispose() $GroupCount = $colResults.Count}Catch { $GroupCount = 0 Write-Host -ForegroundColor red "The $ADSearchBase structure cannot be found!"}if ($GroupCount -ne 0) { write-host -ForegroundColor Green "`nProcessing $GroupCount group objects in the $domain Domain..." $colResults | ForEach-Object { $Name = $_.Properties.name[0] $GroupDN = $_.Properties.distinguishedname[0] $ParentOU = $GroupDN -split '(?<![\\]),' $ParentOU = $ParentOU[1..$($ParentOU.Count-1)] -join ',' $SAMAccountName = $_.Properties.samaccountname[0] Try { $DisplayName = $_.Properties.displayname[0] } Catch { $DisplayName = "" } Try { $Description = $_.Properties.description[0] } Catch { $Description = "" } $GroupType = $_.Properties.grouptype[0] switch($GroupType){ 2 { $GroupCategory = "Distribution" $GroupScope = "Global" $GlobalDistributionGroups = $GlobalDistributionGroups + 1 Break } 4 { $GroupCategory = "Distribution" $GroupScope = "Domain Local" $DomainLocalDistributionGroups = $DomainLocalDistributionGroups + 1 Break } 8 { $GroupCategory = "Distribution" $GroupScope = "Universal" $UniversalDistributionGroups = $UniversalDistributionGroups + 1 Break } -2147483646 { $GroupCategory = "Security" $GroupScope = "Global" $GlobalSecurityGroups = $GlobalSecurityGroups + 1 Break } -2147483644 { $GroupCategory = "Security" $GroupScope = "Domain Local" $DomainLocalSecurityGroups = $DomainLocalSecurityGroups + 1 Break } -2147483643 { $GroupCategory = "Security" $GroupScope = "Builtin Local" $BuiltinLocalSecurityGroups = $BuiltinLocalSecurityGroups + 1 Break } -2147483640 { $GroupCategory = "Security" $GroupScope = "Universal" $UniversalSecurityGroups = $UniversalSecurityGroups + 1 Break } default { $GroupCategory = "Unrecognised" $GroupScope = "Unrecognised" $UnrecognisedGroupTypes = $UnrecognisedGroupTypes + 1 } } $MemberCount = 0 Try { If (($_.Properties.member | Measure-Object).Count -gt 0) { $_.Properties.member | ForEach-Object { $MemberCount = $MemberCount + 1 } } } Catch { # no member count } If ($MemberCount -eq 0) {$TotalNoMembers = $TotalNoMembers + 1} Try { $Mail = $_.Properties.mail[0] } Catch { $Mail = "" } If ($IsExchangePresent) { $MailEnabled = $False Try { If (($_.Properties.proxyaddresses | Measure-Object).Count -gt 0 -AND ($_.Properties.legacyexchangedn | Measure-Object).Count -gt 0 -AND ($_.Properties.mailnickname | Measure-Object).Count -gt 0 -AND $_.Properties.reporttooriginator -eq $True) { $MailEnabled = $True $TotalMailEnabledObjects = $TotalMailEnabledObjects + 1 If ($GroupCategory -eq "Distribution") { $TotalMailEnabledDistributionGroups = $TotalMailEnabledDistributionGroups + 1 } } } Catch { # Not mail-enabled } } $UnixEnabled = $False $GIDNumber = "" Try { If (($_.Properties.gidnumber | Measure-Object).Count -gt 0 -AND ($_.Properties.mssfu30name | Measure-Object).Count -gt 0 -AND ($_.Properties.mssfu30nisdomain | Measure-Object).Count -gt 0) { $UnixEnabled = $True $GIDNumber = $_.Properties.gidnumber[0] $TotalUnixEnabledObjects = $TotalUnixEnabledObjects + 1 } } Catch { # Not Unix enabled } $isCriticalSystemObject = $False Try { If ($_.Properties.iscriticalsystemobject[0] -eq $True) { $isCriticalSystemObject = $True $TotalCriticalSystemObjects = $TotalCriticalSystemObjects + 1 } } Catch { # is not a Critical System Object } Try { If (($_.Properties.admincount| Measure-Object).Count -gt 0) { $AdminCount = $_.Properties.admincount[0] # Use the bitwise-AND (-bAnd) operator to determine if the least significant bit is set (1) or clear (0) $AdminCountLSB = $($_.Properties.admincount[0]) -band 00000001 If ($AdminCountLSB -eq "1") {$TotalProtectedObjects = $TotalProtectedObjects + 1} } Else { $AdminCount = "" $AdminCountLSB = "" } } Catch { # AdminCount not set $AdminCount = "" $AdminCountLSB = "" } $Exclude = $False ForEach ($ExclusionGroup in $ExclusionGroups) { If ($Name -Like $ExclusionGroup) { $Exclude = $True } } ForEach ($ExclusionOU in $ExclusionOUs) { If ($ParentOU -Like $ExclusionOU) { $Exclude = $True } } If ($Exclude) {$TotalExcludedObjects = $TotalExcludedObjects + 1} $Conflict = $False If ($Name -Like "*CNF:*" -OR $_.Properties.samaccountname[0] -Like "`$Duplicate*") { # Replace the Line Feed character in the name so that it's a nicely represented string. $Name = $Name -replace "`n","" $Conflict = $True $TotalConflictingObjects = $TotalConflictingObjects + 1 } If ($MemberCount -eq 0 -AND ($isCriticalSystemObject -eq $True -OR $AdminCountLSB -eq "1" -OR $Exclude)) {$TotalToSubtract = $TotalToSubtract + 1} $SIDHistoryCount = 0 Try { If (($_.Properties.sidhistory | Measure-Object).Count -gt 0) { $_.Properties.sidhistory | ForEach-Object { $SIDHistoryCount = $SIDHistoryCount + 1 } $TotalWithSIDHistory = $TotalWithSIDHistory + 1 } } Catch { # No SID History } $IsManagedBy = $False Try { $ManagedBy = $_.Properties.managedby[0] If ($ManagedBy -ne "" -AND $ManagedBy -ne $NULL) { $IsManagedBy = $True $TotalNoManagedBy = $TotalNoManagedBy + 1 } } Catch { $ManagedBy = "" } $WhenCreated = $_.Properties.whencreated[0] $WhenChanged = $_.Properties.whenchanged[0] If ($IsExchangePresent) { $Expired = $False Try { $ExpirationTime = $_.Properties.expirationtime[0] If ($ExpirationTime -ne $NULL -AND $ExpirationTime -lt (Get-Date)) { $Expired = $True $TotalExpiredObjects = $TotalExpiredObjects + 1 } } Catch { # Has an invalid expirationtime setting $ExpirationTime = "" } } Try { If (($_.Properties.info | Measure-Object).Count -gt 0) { $notes = $_.Properties.info[0] $notes = $notes -replace "`r`n", "|" } else { $notes = "" } } Catch { # No notes set $notes = "" } # Get SID $stringSID = (New-Object System.Security.Principal.SecurityIdentifier($_.Properties.objectsid[0],0)).Value $FullGroupType = "$GroupScope $GroupCategory Group" $obj = New-Object -TypeName PSObject $obj | Add-Member -MemberType NoteProperty -Name "GroupType" -value $FullGroupType # Create a hashtable to capture a count of each Group Type If (!($GroupsHashTable.ContainsKey($FullGroupType))) { $TotalCount = 1 $NoMembersCount = 0 $UnixEnabledCount = 0 $CriticalSystemObjectCount = 0 $ProtectedObjectCount = 0 $ExcludeObjectCount = 0 $ConflictCount = 0 $ContainSIDHistoryCount = 0 $NoManagedByCount = 0 If ($MemberCount -eq 0) {$NoMembersCount = 1} If ($IsManagedBy -eq $False) {$NoManagedByCount = 1} If ($IsExchangePresent) { $MailEnabledCount = 0 $MailDisabledCount = 0 $ExpiredObjectCount = 0 If ($MailEnabled) { $MailEnabledCount = 1 } Else { $MailDisabledCount = 1 } If ($Expired) {$ExpiredObjectCount = 1} } If ($UnixEnabled) { $UnixEnabledCount = 1 } If ($isCriticalSystemObject) {$CriticalSystemObjectCount = 1} If ($AdminCountLSB -eq "1") {$ProtectedObjectCount = 1} If ($Exclude) {$ExcludeObjectCount = 1} If ($Conflict) {$ConflictCount = 1} If ($SIDHistoryCount -ne 0) {$ContainSIDHistoryCount = 1} $obj | Add-Member -MemberType NoteProperty -Name "Total" -value $TotalCount $obj | Add-Member -MemberType NoteProperty -Name "No_Members" -value $NoMembersCount If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "Mail_Enabled" -value $MailEnabledCount $obj | Add-Member -MemberType NoteProperty -Name "Mail_Disabled" -value $MailDisabledCount } $obj | Add-Member -MemberType NoteProperty -Name "Unix_Enabled" -value $UnixEnabledCount $obj | Add-Member -MemberType NoteProperty -Name "Critical_System" -value $CriticalSystemObjectCount $obj | Add-Member -MemberType NoteProperty -Name "Protected" -value $ProtectedObjectCount $obj | Add-Member -MemberType NoteProperty -Name "Conflicting" -value $ConflictCount $obj | Add-Member -MemberType NoteProperty -Name "SIDHistory" -value $ContainSIDHistoryCount $obj | Add-Member -MemberType NoteProperty -Name "No_ManagedBy" -value $NoManagedByCount If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "Expired" -value $ExpiredObjectCount } $obj | Add-Member -MemberType NoteProperty -Name "Excluded" -value $ExcludeObjectCount $GroupsHashTable = $GroupsHashTable + @{$FullGroupType = $obj} } else { $value = $GroupsHashTable.Get_Item($FullGroupType) $TotalCount = $value.Total + 1 $NoMembersCount = $value.No_Members $UnixEnabledCount = $value.Unix_Enabled $CriticalSystemObjectCount = $value.Critical_System $ProtectedObjectCount = $value.Protected $ExcludeObjectCount = $value.Excluded $ConflictCount = $value.Conflicting $ContainSIDHistoryCount = $value.SIDHistory $NoManagedByCount = $value.No_ManagedBy If ($MemberCount -eq 0) {$NoMembersCount = $NoMembersCount + 1} If ($IsManagedBy -eq $False) {$NoManagedByCount = $NoManagedByCount + 1} If ($IsExchangePresent) { $MailEnabledCount = $value.Mail_Enabled $MailDisabledCount = $value.Mail_Disabled $ExpiredObjectCount = $value.Expired If ($MailEnabled) { $MailEnabledCount = $MailEnabledCount + 1 } Else { $MailDisabledCount = $MailDisabledCount + 1 } If ($Expired) {$ExpiredObjectCount = $ExpiredObjectCount + 1} } If ($UnixEnabled) { $UnixEnabledCount = $UnixEnabledCount + 1 } If ($isCriticalSystemObject) {$CriticalSystemObjectCount = $CriticalSystemObjectCount + 1} If ($AdminCountLSB -eq "1") {$ProtectedObjectCount = $ProtectedObjectCount + 1} If ($Exclude) {$ExcludeObjectCount = $ExcludeObjectCount + 1} If ($Conflict) {$ConflictCount = $ConflictCount + 1} If ($SIDHistoryCount -ne 0) {$ContainSIDHistoryCount = $ContainSIDHistoryCount + 1} $obj | Add-Member -MemberType NoteProperty -Name "Total" -value $TotalCount $obj | Add-Member -MemberType NoteProperty -Name "No_Members" -value $NoMembersCount If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "Mail_Enabled" -value $MailEnabledCount $obj | Add-Member -MemberType NoteProperty -Name "Mail_Disabled" -value $MailDisabledCount } $obj | Add-Member -MemberType NoteProperty -Name "Unix_Enabled" -value $UnixEnabledCount $obj | Add-Member -MemberType NoteProperty -Name "Critical_System" -value $CriticalSystemObjectCount $obj | Add-Member -MemberType NoteProperty -Name "Protected" -value $ProtectedObjectCount $obj | Add-Member -MemberType NoteProperty -Name "Conflicting" -value $ConflictCount $obj | Add-Member -MemberType NoteProperty -Name "SIDHistory" -value $ContainSIDHistoryCount $obj | Add-Member -MemberType NoteProperty -Name "No_ManagedBy" -value $NoManagedByCount If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "Expired" -value $ExpiredObjectCount } $obj | Add-Member -MemberType NoteProperty -Name "Excluded" -value $ExcludeObjectCount $GroupsHashTable.Set_Item($FullGroupType,$obj) } $obj = $Null $obj = New-Object -TypeName PSObject $obj | Add-Member -MemberType NoteProperty -Name "Name" -value $Name $obj | Add-Member -MemberType NoteProperty -Name "ParentOU" -value $ParentOU $obj | Add-Member -MemberType NoteProperty -Name "sAMAccountName" -value $SAMAccountName $obj | Add-Member -MemberType NoteProperty -Name "DisplayName" -value $DisplayName $obj | Add-Member -MemberType NoteProperty -Name "Description" -value $Description $obj | Add-Member -MemberType NoteProperty -Name "MemberCount" -value $MemberCount $obj | Add-Member -MemberType NoteProperty -Name "GroupCategory" -value $GroupCategory $obj | Add-Member -MemberType NoteProperty -Name "GroupScope" -value $GroupScope $obj | Add-Member -MemberType NoteProperty -Name "Mail" -value $Mail If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "MailEnabled" -value $MailEnabled } $obj | Add-Member -MemberType NoteProperty -Name "isCriticalSystemObject" -value $isCriticalSystemObject $obj | Add-Member -MemberType NoteProperty -Name "AdminCount" -value $AdminCount $obj | Add-Member -MemberType NoteProperty -Name "Exclude" -value $Exclude If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "Expired" -value $Expired } $obj | Add-Member -MemberType NoteProperty -Name "Conflicting" -value $Conflict $obj | Add-Member -MemberType NoteProperty -Name "managedBy" -value $ManagedBy If ($IsExchangePresent) { $obj | Add-Member -MemberType NoteProperty -Name "ExpirationTime" -value $ExpirationTime } $obj | Add-Member -MemberType NoteProperty -Name "WhenChanged" -value $WhenChanged $obj | Add-Member -MemberType NoteProperty -Name "WhenCreated" -value $WhenCreated $obj | Add-Member -MemberType NoteProperty -Name "SIDHistoryCount" -value $SIDHistoryCount $obj | Add-Member -MemberType NoteProperty -Name "UnixEnabled" -value $UnixEnabled $obj | Add-Member -MemberType NoteProperty -Name "GIDNumber" -value $GIDNumber $obj | Add-Member -MemberType NoteProperty -Name "info" -value $notes $obj | Add-Member -MemberType NoteProperty -Name "objectsid" -value $stringSID # PowerShell V2 doesn't have an Append parameter for the Export-Csv cmdlet. Out-File does, but it's # very difficult to get the formatting right, especially if you want to use quotes around each item # and add a delimeter. However, we can easily do this by piping the object using the ConvertTo-Csv, # Select-Object and Out-File cmdlets instead. if ($PSVersionTable.PSVersion.Major -gt 2) { $obj | Export-Csv -Path "$ReferenceFileFull" -Append -Delimiter $Delimiter -NoTypeInformation -Encoding ASCII } Else { if (!(Test-Path -path $ReferenceFileFull)) { $obj | ConvertTo-Csv -NoTypeInformation -Delimiter $Delimiter | Select-Object -First 1 | Out-File -Encoding ascii -filepath "$ReferenceFileFull" } $obj | ConvertTo-Csv -NoTypeInformation -Delimiter $Delimiter | Select-Object -Skip 1 | Out-File -Encoding ascii -filepath "$ReferenceFileFull" -append -noclobber } $obj = $Null $TotalGroupsProcessed ++ If ($ProgressBar) { Write-Progress -Activity 'Processing Groups' -Status ("Count: $($TotalGroupsProcessed) - Name: {0}" -f $Name) -PercentComplete (($TotalGroupsProcessed/$GroupCount)*100) } } # Dispose of the search and results properly to avoid a memory leak $colResults.Dispose() # Remove the quotes from the output file. If ($RemoveQuotesFromCSV) { (get-content "$ReferenceFileFull") |% {$_ -replace '"',""} | out-file "$ReferenceFileFull" -Fo -En ascii } write-host -ForegroundColor Green "`nA breakdown of the $GroupCount Group Objects in the $domain Domain:" $Output = $GroupsHashTable.values | ForEach {$_ } | ForEach {$_ } | Sort-Object GroupType -descending # Auto-sized tables are by default limited to the width of your screen buffer. So to # ensure all columns of the table are displayed we force it to 4096 characters. I also # find that the Format-Table cmdlet will output a maximum of 10 columns by default, so # you must use the "Property" parameter and set it to *. $Output | Format-Table -Property * -AutoSize | Out-String -Width 4096 # Write-Output $Output | Format-Table $Output | Export-Csv -Path "$ReferenceFileSummary" -Delimiter $Delimiter -NoTypeInformation # Remove the quotes If ($RemoveQuotesFromCSV) { (get-content "$ReferenceFileSummary") |% {$_ -replace '"',""} | out-file "$ReferenceFileSummary" -Fo -En ascii } # Note that for the summary output I went with a hashtable instead of binding multiple objects together. # Whilst some of the code may seem excessive and repetitive, I found this the simplest method to achieve # the desired output. $SummaryHashTable = @{} $Item = 0 $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($GlobalDistributionGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Global Distribution Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $GlobalDistributionGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Global Distribution Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($DomainLocalDistributionGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Domain Local Distribution Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $DomainLocalDistributionGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Domain Local Distribution Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($UniversalDistributionGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Universal Distribution Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $UniversalDistributionGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Universal Distribution Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($GlobalSecurityGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Global Security Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $GlobalSecurityGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Global Security Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($DomainLocalSecurityGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Domain Local Security Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $DomainLocalSecurityGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Domain Local Security Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($BuiltinLocalSecurityGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Builtin Local Security Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $BuiltinLocalSecurityGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Builtin Local Security Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($UniversalSecurityGroups/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Universal Security Groups" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $UniversalSecurityGroups $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Universal Security Groups" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($UnrecognisedGroupTypes/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Unrecognised Group Type" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $UnrecognisedGroupTypes $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Unrecognised Group Type" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalNoMembers/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups with no members" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalNoMembers $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups with no members" = $Summaryobj} $Summaryobj = $Null If ($IsExchangePresent) { $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalMailEnabledObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that are mail-enabled" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalMailEnabledObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that are mail-enabled" = $Summaryobj} $Summaryobj = $Null } $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalUnixEnabledObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that are Unix-enabled" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalUnixEnabledObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that are Unix-enabled" = $Summaryobj} $Summaryobj = $Null If ($IsExchangePresent) { $Summaryobj = New-Object -TypeName PSObject $TotalDistributionGroups = $GlobalDistributionGroups + $DomainLocalDistributionGroups + $UniversalDistributionGroups $percent = "{0:P}" -f (($TotalDistributionGroups - $TotalMailEnabledDistributionGroups)/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Distribution Groups that are mail-disabled" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value ($TotalDistributionGroups - $TotalMailEnabledDistributionGroups) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Distribution Groups that are mail-disabled" = $Summaryobj} $Summaryobj = $Null } $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalCriticalSystemObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that are critical system objects" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalCriticalSystemObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that are critical system objects" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalProtectedObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that are protected objects (AdminSDHolder)" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalProtectedObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that are protected objects (AdminSDHolder)" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalExcludedObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that are marked as excluded objects" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalExcludedObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that are marked as excluded objects" = $Summaryobj} $Summaryobj = $Null If ($IsExchangePresent) { $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalExpiredObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that have expired" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalExpiredObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that have expired" = $Summaryobj} $Summaryobj = $Null } $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f (($TotalNoMembers - $TotalToSubtract)/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups with no members that are not critical system, protected, or excluded objects" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value ($TotalNoMembers - $TotalToSubtract) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups with no members that are not critical system, protected, or excluded objects" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalConflictingObjects/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups that are conflicting/duplicate objects" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalConflictingObjects $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups that are conflicting/duplicate objects" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalWithSIDHistory/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups with SID history" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalWithSIDHistory $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups with SID history" = $Summaryobj} $Summaryobj = $Null $Summaryobj = New-Object -TypeName PSObject $percent = "{0:P}" -f ($TotalNoManagedBy/$GroupCount) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Item" -value ($Item = $Item + 1) $Summaryobj | Add-Member -MemberType NoteProperty -Name "Statement" -value "Groups with no Manager (managedBy)" $Summaryobj | Add-Member -MemberType NoteProperty -Name "Total_Count" -value $TotalNoManagedBy $Summaryobj | Add-Member -MemberType NoteProperty -Name "Overall_Percentage" -value $percent $SummaryHashTable = $SummaryHashTable + @{"Groups with no Manager (managedBy)" = $Summaryobj} $Summaryobj = $Null write-host -ForegroundColor Green "Summary Totals:" $Output = $SummaryHashTable.values | ForEach {$_ } | ForEach {$_ } | Sort-Object Item $Output | Format-Table -AutoSize # Write-Output $Output | Format-Table $Output | Export-Csv -Path "$ReferenceFileSummaryTotals" -Delimiter $Delimiter -NoTypeInformation # Remove the quotes If ($RemoveQuotesFromCSV) { (get-content "$ReferenceFileSummaryTotals") |% {$_ -replace '"',""} | out-file "$ReferenceFileSummaryTotals" -Fo -En ascii } write-host "Notes:" -foregroundColor Yellow write-host " - Disabling groups:" -foregroundColor Yellow write-host " - Security groups can be disabled by converting them to a distribution group." -foregroundColor Yellow write-host " - Distribution groups can be disabled by mail-disabling them." -foregroundColor Yellow write-host " You should always clearly document situations where groups have been disabled. i.e.`n Are they being kept for a reason, or should they be deleted. Delete them if they no`n longer serve a purpose." -foregroundColor Yellow write-host " - You should never delete groups marked as Critical System Objects." -foregroundColor Yellow write-host " - Some groups may simply be placeholders for certain tasks, scripts and policies, and`n therefore may purposely not contain any members. Simply move these groups into an OU and`n add the OU to the `$ExclusionOUs array to flag and exclude them from the final no members`n count when this script is re-run." -foregroundColor Yellow write-host " - In general add groups and OUs to the 'Exclusion' arrays to flag and exclude groups`n with no members from the final no members count." -foregroundColor Yellow write-host " - Review the value of groups that contain no members, are not critical system objects,`n protected objects (AdminSDHolder), and not excluded objects. Delete them if they are no`n longer serving their purpose. Alternatively, move them into an OU and add the OU to the`n `$ExclusionOUs array." -foregroundColor Yellow write-host " - Review the groups that have been marked as protected objects (AdminSDHolder) that may`n now fall out of scope. If these groups are not going to be deleted, they should be`n restored to their original state by reactivating the inheritance rights on the object`n itself and clearing the adminCount attribute." -foregroundColor Yellow write-host " - There should be no groups with an unrecognised group type. But if there are any, they`n must be investigated and remediated immediately as they could be the result of more`n serious issues." -foregroundColor Yellow write-host " - Groups whose name contains CNF: and/or sAMAccountName contains `$Duplicate means that`n it's a duplicate account caused by conflicting/duplicate objects. This typically occurs`n when objects are created on different Read Write Domain Controllers at nearly the same`n time. After replication kicks in and those conflicting/duplicate objects replicate to`n other Read Write Domain Controllers, Active Directory replication applies a conflict`n resolution mechanism to ensure every object is and remains unique. You can't just delete`n the conflicting/duplicate objects, as these may often be in use. You need to merge the`n group membership and ensure the valid group is correctly applied to the resource. Then`n you can confidently delete the conflicting/duplicate group." -foregroundColor Yellow If ($IsExchangePresent) { write-host " - A nice way to manage groups is to set their expirationTime attribute. This will give`n us the ability to implement a nice life cycle management process. You can go one step`n further and add a user or mail enabled security group to the managedBy attribute. This`n will give us the ability to implement some workflow when the group is x days before`n expiring." -foregroundColor Yellow } Else { write-host " - Unfortunately the Exchange Schema Extensions have not been deployed to this forest,`n which means that you don't have access to use the expirationTime attribute to manage`n the life cycle of the group." -foregroundColor Yellow } write-host "`nCSV files to review:" -foregroundColor Yellow write-host " - $ReferenceFileFull" -foregroundColor Yellow write-host " - $ReferenceFileSummary" -foregroundColor Yellow write-host " - $ReferenceFileSummaryTotals" -foregroundColor Yellow} |
Enjoy!